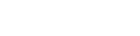
Looking at the cyber threats posed by nation states, organisations must assess their own risk and prioritise defences against them accordingly
Russia has long been regarded as notorious for international cyber threats, and this has only accelerated during 2022, as Ukraine has received an onslaught of online attacks ahead of a physical invasion.
In today’s geopolitical climate, however, there’s more than one nation state player where cyber threats will emerge.
Ultimately, for Western “Five Eyes” organisations – those in the UK, US, Australia, Canada, and New Zealand – the state actors most likely deemed as threats are Russia, China, Iran and North Korea.
Whilst we often focus on the individual capabilities of states themselves, we should be reminded that many criminal organisations carry out attacks either on behalf of nation states or under the protection of them.
Goals of the states and criminal gangs – and the risks they pose
The aims of these malicious actors are wide-ranging – from the theft of intellectual property, intelligence gathering or even the disruption of another nation’s critical infrastructure.
But the bottom line is they will be looking to gain an upper hand, whether to develop technology, increase their country’s financial leverage or disrupt another nation’s means of defending itself.
Where cyber criminal organisations are used, their aim is almost always to profit financially – but a nation state may specify the targets they’ll turn a blind eye to, or which should be a priority. In some cases where there are economic sanctions on the nation state, they may also demand some of the profit be redistributed to the state itself.
Whilst we often talk about large-scale cyber attacks against critical national infrastructure, we shouldn’t ignore one of the most common aims of nation states in the past few years – to spread misinformation.
This has recently been demonstrated as a means of disrupting the democratic process in a way that favours that state, or once again enables them to profit financially.
These types of attacks are much harder to measure in terms of the scale and impact
These types of attacks are much harder to measure in terms of the scale and impact, but we can’t overlook the potential influence these assaults have had on the world over the last several years.
Large organisations considered critical national infrastructure are at risk of being targeted by state actors (often referred to as advanced persistent threats) but, as seen in recent years, any organisation can be a victim of a nation state attack even if they aren’t targeted.
It may be that they become collateral damage after being vulnerable to a particular attack vector that the state is using, or that part of their supply chain has been compromised.
The proliferation of tools used by criminal groups will have a big impact, not just as a result of professional attacks, but due to smaller and less skilled hackers having more accessibility to the same methods. As such, the number of organisations that might be attacked will increase.
Protective measures for organisations to take
It should be made clear there’s no single biggest threat in terms of the nation state because the landscape, objectives and capabilities of each actor change so quickly.
Focusing on one single nation state when it’s far more likely to be attacked by a criminal organisation will only create a false sense of security. Organisations must assess their own risk against the main threat actors and, in calculating the threats, they can prioritise defences against them accordingly.
Enabling protections such as firewalls and endpoint security are key for all organisations to maintain
Getting the basics right will go a long way in creating a foundation of cyber threat protection, no matter whether that’s an attack from criminals or a state. The strategy should ensure that security and IT teams patch regularly alongside good identity and password management, and configuration of endpoints and networks against best practices. Enabling protections such as firewalls and endpoint security are also key for all organisations to maintain.
Additionally, ensuring your organisation can react quickly and sensibly if it’s compromised is essential. This means it’s important to have good backups that have been tested and are resilient to malware such as ransomware, as well as implementing good incident response and crisis management procedures.
Preparing for the future
Looking ahead at the cyber threat landscape, we should expect to experience more of the same as this approach has proved highly successful. There’s no need for a nation state to reveal their capabilities, or use a capability that once revealed can no longer be used if they can continue to impact other nations by proxy through criminal cyber organisations.
Instead, they focus their attacks on things that are less obvious – gaining persistent access to an organisation’s networks to gather intelligence or steal intellectual property for example.
We’ve seen a recent increase in supply chain attacks and that’s likely to increase as more organisations seek to benefit from larger offerings, whether that be software or services, as the impact of compromising a single organisation can have a much wider impact.
In particular, we’ve seen an increase in attacks against vulnerable infrastructure such as routers and other internet-facing infrastructure that haven’t been maintained or are effectively end of life. Whilst many organisations have vulnerable internet-facing infrastructure or networks that are insecure once an attacker achieves initial entry, attackers need not necessarily use their advanced capabilities.
Criminal activity by its nature seeks to exact profit and the use of cryptocurrency may help to circumvent sanctions and other restrictions
We may very well see an increase in attacks by actors associated with Russia if economic sanctions continue. Criminal activity by its nature seeks to exact profit and the use of cryptocurrency may help to circumvent sanctions and other restrictions.
Whatever the future may present, organisations must remain as vigilant, collaborative and agile as possible – working as a secure unit internally and with external partners in order to protect against cyber threats from nation states and their accomplices.
This piece was written and provided by Steve Forbes, a government cyber security expert at Nominet.