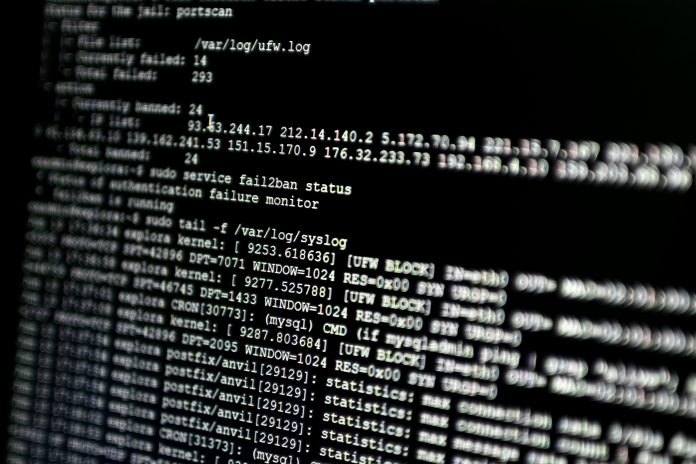
New research from the BlackBerry Cylance Threat Intelligence Team has uncovered a trove of highly sensitive data, suggesting an increased cybercrime risk
Included in the report is confidential information detailing aspects of a country’s civilian air traffic control system in a semi-public malware repository, the apparent by-product of penetration testing, one of a number of startling findings.
In Thin Red Line: Penetration Testing Practices Examined, the BlackBerry Cylance Threat Intelligence Team sheds light on a range of questionable pentesting practices, by-products and outcomes. The report raises critical questions about the industry’s adherence to expectations of privacy and confidentiality, as well as compliance with legal and regulatory requirements, like Europe’s General Data Protection Regulation (GDPR).
Included in the report is a case study of an advanced persistent threat (APT) like group which the research team found to be operating openly as a Brazilian security firm that is linked to the exposure of sensitive air traffic control data. This revelation is one of a number of findings in the report that demonstrate how the line distinguishing pentesting exercises from actual threat actor behaviour has thinned.
“Though many of our findings are uncomfortable, we are sharing this research in order to start a conversation we hope will help better educate security researchers, pentesters, and the clients they both seek to serve,” says Kevin Livelli, Director of Threat Intelligence at BlackBerry Cylance.
“We must hold ourselves accountable to each other and to ourselves to ensure that we remain good stewards for those who rely on our support – and be deserving of their trust.”
The research also explores the tradecraft of more than two dozen well-known companies offering pentesting services, from boutiques to blue chips, and finds the widespread exposure of client data in semi-public repositories.
Josh Lemos, VP of Research and Intelligence at BlackBerry Cylance said:
“Over the past five years the explosion of groups around the globe offering offensive testing services has led to practices that can materially compromise a company’s security posture.
“We want this report to help the security community, and the clients they serve, think more critically about how red teaming operations can impact security, agree to guiding principles for engagements such as data handling, and bring awareness to dangerous testing practices, inadvertent or not.”
Download the Thin Red Line: Penetration Testing Practices Examined report here.