Toby Griffiths, Head of Innovation and Delivery for NHS Digital’s Data Security Centre, discusses how NHS Digital tackled cyber security issues and how ‘security debt’ brought about by the pandemic is being addressed
The pandemic posed many challenges across the NHS, from capacity and supply chain through to staffing. However, what is not as often spoken about is the marked increase in activity from hostile threat actors in the cyberspace.
During the pandemic, there was a 44% rise in ransomware attacks alone across the health sector, while other sectors faced a 22% increase.
Healthcare remains a prime target to criminal gangs and hostile states, although attacks have tended to be aimed at private health in other countries and not at the NHS itself. If the NHS is impacted by attacks, it has historically been as a victim of broader activity rather than a focused attack on UK healthcare.
Attacks on other sectors, however, still have the potential to inadvertently impact the NHS. This, in turn, has obvious impacts on patient care and results in high remediation and clean-up costs.
The Data Security Centre worked very closely throughout the pandemic with expert colleagues in NHSX and the NCSC to formalise a ‘Cyber COVID-19 response’ work plan to help support frontline organisations reduce risks to people, processes and technology.
Demand for our services increased, and we had to adopt a flexible approach, both to relieve frontline operational pressures and to support those accountable for good cyber security within their organisation to have the confidence and assurance that they had the right controls and processes in place.
Support for the front line
We knew that many people experienced a transformative change as they moved to remote working and that this could introduce new vulnerabilities. That’s why one of our first priorities was to publish guidance on how to work from home securely, first internally to colleagues within NHS Digital, then to the wider NHS.
We also established a Technical Remediation Service to provide frontline organisations with specialist support to identify critical vulnerabilities in their technology and processes. We worked closely with NHSX to ensure that organisations had access to funding to replace vulnerable or out-of-date technology.
Our focus was on ensuring organisations had the right processes and controls in place for backing up data. This is particularly important during a pandemic, as the increase in ransomware attacks can take systems offline so there needs to be a failsafe.
The service was also able to offer more bespoke specialist support that met individual organisations’ needs where they already knew their vulnerabilities.
This service carried on in 2021, so we continued to address the most serious challenges around backups and ensure organisations have the right controls in place on their highly valuable Active Directory.
“Healthcare remains a prime target to criminal gangs and hostile states, although attacks have tended to be aimed at private health in other countries and
not at the NHS itself.”
The Active Directory enables administrators to manage permissions and access to network resources so, if compromised, it could be used to spy on the system, escalate privileges and access data on an organisation’s infrastructure, which is why it is often termed the ‘keys to the kingdom’ for an attacker.
However, the technical remediation service was not the only service in demand by NHS organisations over the last eighteen months. Our incident response service from the Security Operations Centre was strengthened throughout the pandemic to support organisations to get back up and running as quickly as possible, after experiencing an incident.
This bolstering of the service was crucial as we saw a 147% increase in the number of external incidents supported over a comparative six-month period from 2019 to 2020, and we were able to respond quickly to support these incidents when they occurred.
Collaborative partnership working to keep the pandemic response safe
Behind the scenes, we supported NHS Test & Trace by establishing a standalone Security Operations Centre to provide dedicated threat intelligence and incident response so they could securely deliver the critical work of managing the spread of the virus.
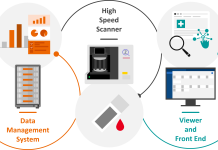
Meanwhile, this was supported by the national SOC, which had visibility and monitoring on data feeds from critical national technology services, such as COVID App, DaSH (Data Science Hub), National Booking Service, and NHS App, enabling us to proactively detect threats and incidents.
Our specialist security services team also provided security assurance on the technical infrastructure that supported the rollout of vaccinations to the general public. Compromise of these systems could have been catastrophic to the government’s rollout plan of vaccinations vital in the fight against COVID-19.
Tackling the security debt
As you might imagine, all of this was delivered at pace by a combination of teams from different organisations in the NHS, to try and stay ahead of the security risks that we saw increasing during the pandemic. These risks were real and important, and the work to address them was crucial to keep systems and organisations safe.
However, at the same time, the pandemic also created extreme pressure on NHS organisations.
This led to something called security debt, which resulted from cyber security concerns often taking a back seat in NHS organisations as they were faced with an exponential increase in patients needing care.
Security debt results in risks and vulnerabilities to the infrastructure that supports healthcare, and so as we emerge from the pandemic, we need to remind people why good cyber security is so crucial to the effective running of a hospital or a trust.
With this in mind, we and our partners are working closely with NHS trusts and organisations, to provide them with the support and guidance that will help them reinforce their systems and processes. We have also relaunched our Keep IT Confidential campaign with even more content, which provides training tools for staff to teach good cyber hygiene, the basics that every staff member can be responsible for to help keep their organisation and data secure.
The pandemic has certainly tested our capabilities and those of organisations across the sector. However, through collaborative working with our partners and targeted reinforcement of key services, we have helped the sector stay secure while they battled a global pandemic on the front lines.